Burp scanner reference for STO
You can scan your application instances using Burp Enterprise.
Important notes for running Burp scans in STO
Root access requirements
You need to run the scan step with root access if either of the following apply:
-
You need to run a Docker-in-Docker background service.
-
You need to add trusted certificates to your scan images at runtime.
You can set up your STO scan images and pipelines to run scans as non-root and establish trust for your own proxies using self-signed certificates. For more information, go to Configure STO to Download Images from a Private Registry.
For more information
The following topics contain useful information for setting up scanner integrations in STO:
Burp step settings for STO scans
The recommended workflow is add a Burp step to a Security Tests or CI Build stage and then configure it as described below.
Scan
Scan Mode
- Orchestration Configure the step to run a scan and then ingest, normalize, and deduplicate the results.
- Extraction Configure the step to extract scan results from an external SaaS service and then ingest, normalize, and deduplicate the data.
- Ingestion Configure the step to read scan results from a data file and then ingest, normalize, and deduplicate the data.
Scan Configuration
The predefined configuration to use for the scan. All scan steps have at least one configuration.
The following configurations are available for Orchestration scans. These are built-in configurations provided by Burp Enterprise.
DefaultThis is the same as theCrawl and Audit - Lightweightbuilt-in configuration.Never stop Crawl due to application errorsNever stop audit due to application errorsMinimize false positivesMinimize false negativesCrawl strategy most completeCrawl strategy more completeCrawl strategy fastestCrawl strategy fasterCrawl limit 60 minutesCrawl limit 30 minutesCrawl limit 10 minutesCrawl and audit lightweightCrawl and audit fastCrawl and audit deepCrawl and audit balancedAudit coverage thoroughAudit coverage maximumAudit checks medium activeAudit checks light activeAudit checks critical issues onlyAudit checks all except time based detection methodsAudit checks all except java script analysis
Target
Type
- Instance Scan a running application.
Name
The identifier for the target, such as codebaseAlpha or jsmith/myalphaservice. Descriptive target names make it much easier to navigate your scan data in the STO UI.
It is good practice to specify a baseline for every target.
Variant
The identifier for the specific variant to scan. This is usually the branch name, image tag, or product version. Harness maintains a historical trend for each variant.
Authentication
Domain
Domain of the application instance to scan. Example: https://myapp.io/portal/us
Access Token
The access token used to log in to a specific product in the scanner. This is required for some scans. In most cases, this is a password or an API key.
You should create a Harness text secret with your encrypted token and reference the secret using the format <+secrets.getValue("project.container-access-id")>. For more information, go to Add and Reference Text Secrets.
Scan Tool
Use this setting to specify a specific scan to ingest. If this is not specified, the pipeline ingests the most recent scan.
Instance
Domain
Domain of the application instance to scan. You can include the full path to the app in this field, or split the full path between the Domain and the Path fields. Example: https://myapp.io/portal/us
Protocol
HTTPS (default) or HTTP.
Port
The TCP port used by the scanned app instance.
Path
Path to append to the application instance domain, if you're splitting the full path between the Domain and Path settings. For example, you might specify the domain as https://myapp.io and the path as /portal/us.
Username
Username to log in to the instance you want to scan.
Password
The access token to log in to the instance you want to scan. In most cases, this is a password or an API key.
You should create a Harness text secret with your encrypted token and reference the secret using the format <+secrets.getValue("project.container-access-id")>. For more information, go to Add and Reference Text Secrets.
Ingestion File
The path to your scan results when running an Ingestion scan, for example /shared/scan_results/myscan.latest.sarif.
-
The data file must be in a supported format for the scanner.
-
The data file must be accessible to the scan step. It's good practice to save your results files to a shared path in your stage. In the visual editor, go to the stage where you're running the scan. Then go to Overview > Shared Paths. You can also add the path to the YAML stage definition like this:
- stage:
spec:
sharedPaths:
- /shared/scan_results
Security step settings for Burp scans in STO (legacy)
You can set up Burp scans using a Security step, but this is a legacy functionality. Harness recommends that you use a Burp step instead.
Target and variant
The following settings are required for every Security step:
target_nameA user-defined label for the code repository, container, application, or configuration to scan.variantA user-defined label for the branch, tag, or other target variant to scan.
Make sure that you give unique, descriptive names for the target and variant. This makes navigating your scan results in the STO UI much easier.
You can see the target name, type, and variant in the Test Targets UI:
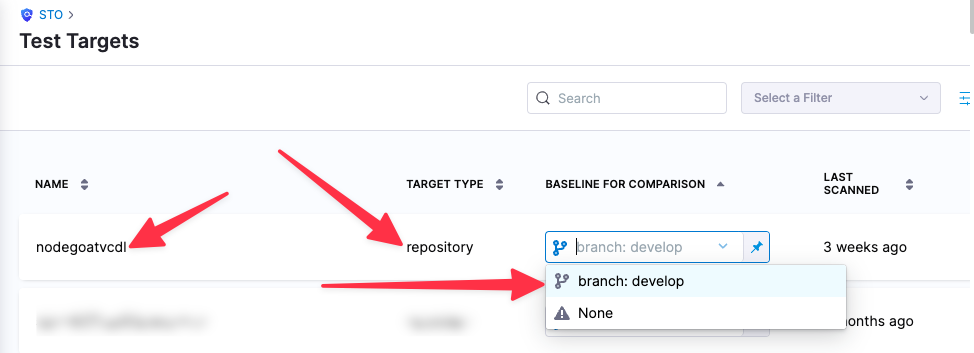
For more information, go to Targets, baselines, and variants in STO.
Burp scan settings
product_name=burpscan_type=instancepolicy_type=orchestratedScan,dataLoad, oringestionOnlyproduct_config_name- The following configurations are available. These are built-in configurations provided by Burp Enterprise.
defaultThis is the same as theCrawl and Audit - Lightweightbuilt-in configuration.never-stop-crawl-due-to-application-errorsnever-stop-audit-due-to-application-errorsminimize-false-positivesminimize-false-negativescrawl-strategy-most-completecrawl-strategy-more-completecrawl-strategy-fastestcrawl-strategy-fastercrawl-limit-60-minutescrawl-limit-30-minutescrawl-limit-10-minutescrawl-and-audit-lightweightcrawl-and-audit-fastcrawl-and-audit-deepcrawl-and-audit-balancedaudit-coverage-thoroughaudit-coverage-maximumaudit-checks-medium-activeaudit-checks-light-activeaudit-checks-critical-issues-onlyaudit-checks-all-except-time-based-detection-methodsaudit-checks-all-except-java-script-analysis
- The following configurations are available. These are built-in configurations provided by Burp Enterprise.
fail_on_severity- See Fail on Severity.
Instance scan settings
The following settings apply to Security steps where the scan_type is instance.
instance_domaininstance_pathinstance_protocolinstance_portinstance_usernameThe username for authenticating with the external scanner.instance_passwordYou should create a Harness text secret with your encrypted password and reference the secret using the format<+secrets.getValue("project.container-access-id")>. For more information, go to Add and reference text secrets.
Orchestration scan settings
The following settings are required for Security steps where the policy_type is orchestratedScan.
-
product_domainDomain of the application instance to scan. You can include the full path to the app in this field, or split the full path between the Domain and the Path fields. Example:https://myapp.io/portal/us -
product_access_tokenThe access token used to log in to a specific product in the scanner. This is required for some scans. In most cases this is a password or an API key.You should create a Harness text secret with your encrypted token and reference the secret using the format
<+secrets.getValue("project.container-access-id")>. For more information, go to Add and Reference Text Secrets.
For a complete workflow description and example, go to Run an Orchestration Scan in an STO Pipeline.
Dataload scan settings
The following settings are required for Security steps where the policy_type is dataLoad.
-
product_site_idThe Burp enterprise site identifier. -
product_domainDomain of the application instance to scan. Example:https://myapp.io/portal/usYou need to specify either the
product_site_idor theproduct_domain. -
product_scan_idUse this setting to specify a specific scan to ingest. If this is not specified, the pipeline will ingest the most recent scan. -
product_access_tokenThe access token used to log in to a specific product in the scanner. This is required for some scans. In most cases this is a password or an API key.You should create a Harness text secret with your encrypted token and reference the secret using the format
<+secrets.getValue("project.container-access-id")>. For more information, go to Add and Reference Text Secrets.
Ingestion file
If the policy_type is ingestionOnly:
ingestion_file= The path to your scan results when running an Ingestion scan, for example/shared/scan_results/myscan.latest.sarif.
-
The data file must be in a supported format for the scanner.
-
The data file must be accessible to the scan step. It's good practice to save your results files to a shared path in your stage. In the visual editor, go to the stage where you're running the scan. Then go to Overview > Shared Paths. You can also add the path to the YAML stage definition like this:
- stage:
spec:
sharedPaths:
- /shared/scan_results
Fail on Severity
Every Security step has a Fail on Severity setting. If the scan finds any vulnerability with the specified severity level or higher, the pipeline fails automatically. You can specify one of the following:
CRITICALHIGHMEDIUMLOWINFONONE— Do not fail on severity
The YAML definition looks like this: fail_on_severity : critical # | high | medium | low | info | none